20 Pro Tips For Deciding On Shielded Websites
Wiki Article
"The Zk-Powered Shield" What Zk-Snarks Hide Your Ip And Personal Information From The Public
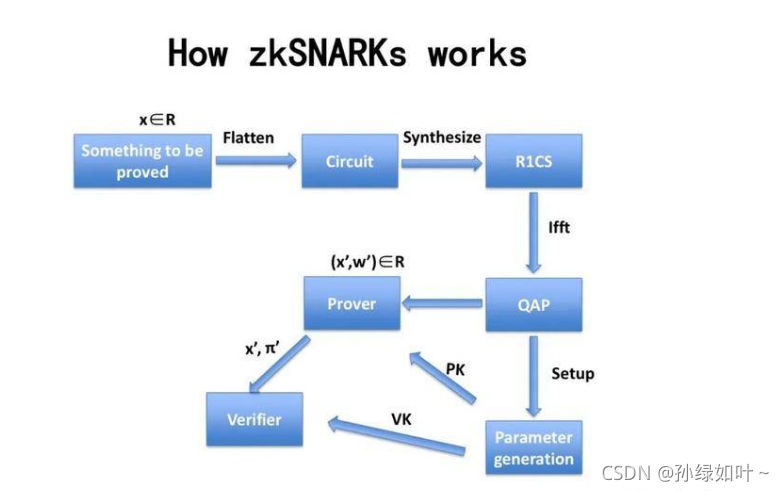
Over the years, privacy software were based on a notion of "hiding among the noise." VPNs funnel you through a server; Tor redirects you to other multiple nodes. While they are useful, they are essentially obfuscation--they hide the origin by shifting it instead of proving it cannot be exposed. zk-SNARKs (Zero-Knowledge Succinct, Non-Interactive Arguments of Knowledge) introduce a totally different way of thinking: you must prove you're authorized to take an action, without divulging who the authorized person that. It is possible to prove this in Z-Text. you can broadcast a message directly to BitcoinZ blockchain, and the blockchain can confirm that you're a legitimate participant with an active shielded identity, however, it is not able to determine the individual address it was that broadcasted to. Your IP address, the identity of you is not known, and the existence of you in the conversation becomes mathematically unknowable to anyone who observes, but confirmed to the protocol.
1. The Dissolution Of the Sender-Recipient Link
It is true that traditional communication, even with encryption, reveals the connection. One observer notices "Alice is conversing with Bob." Zk-SNARKs cause this to break completely. If Z-Text emits a shielded signal an zk proof confirms there is a valid transaction--that's right, the sender has sufficient balance and that the keys are valid--without divulging details about the address sent by the sender or the recipient's address. To an outside observer, the transaction will appear as a sound wave that originates generated by the network, in contrast to any one particular participant. The relationship between two humans becomes computationally unattainable to establish.
2. IP Security of Addresses at the Protocol Level, but not at the App Level
VPNs and Tor provide protection for your IP by routing data through intermediaries. However these intermediaries will become a new source of trust. Z-Text's use for zk SARKs signifies your IP's location is never relevant to transaction verification. In broadcasting your signal protected to the BitcoinZ peer-to-peer network, you are among thousands of nodes. The zk-proof assures that even there is an eye-witness who watches Internet traffic, they're unable to match the message being sent and the wallet or account that is the originator, as the certificate doesn't hold that information. The IP disappears into noise.
3. The Abolition of the "Viewing Key" Discourse
In most privacy-focused blockchains the user has"viewing key "viewing key" capable of decrypting transaction information. Zk's-SNARKs which are implemented within Zcash's Sapling protocol used by Z-Text, permit selective disclosure. A person can demonstrate that you've sent an email with no divulging your IP or your other transactions, or even the exact content that message. The evidence is solely being shared. This kind of control is impossible for IP-based systems because revealing messages automatically reveal the origin address.
4. Mathematical Anonymity Sets That Scale Globally
In a mixing system or a VPN in a mixing service or a VPN, your anonymity is not available to all other users in the specific pool at that time. With zk-SNARKs, your anonymity established is all shielded addresses of the BitcoinZ blockchain. Because the verification proves it is indeed a protected address from the potential of millions of others, and does not give any clue as to which one, your security is a part of the network. It isn't just a small room of peers that are scattered across the globe, but in an international community of cryptographic identifications.
5. Resistance to Attacks on Traffic Analysis and Timing attacks
Ingenious adversaries don't read IPs; they analyze trends in traffic. They analyze who is sending information at what times, and compare to the exact timing. Z-Text's use of zk-SNARKs, as well as a blockchain mempool allows the decoupling actions from broadcast. The ability to build a proof offline and then broadcast it when a server is ready to relay the proof. When you broadcast a proof, the time it was made for its incorporation into a block not necessarily correlated with the instant you made it. breaking the timing analysis process that frequently blocks simpler anonymity methods.
6. Quantum Resistance via Hidden Keys
It is not a quantum security feature in the sense that if a hacker can capture your information now but later crack the encryption they could link the data to you. Zk-SNARKs, which are used in Z-Text can shield your keys themselves. The key that you share with the world is never publicized on the blockchain, since your proof of identity confirms you have the correct key without having to show it. A quantum computing device, one day, will look only at the proof and not the key. Your communications from the past remain confidential because the key used to make them sign was never made available to be hacked.
7. The unlinkable identity of multiple conversations
With a single wallet seed allows you to create multiple secured addresses. Zk-SNARKs enable you to demonstrate that you have one of those addresses without revealing which one. The result is that you'll have many conversations with distinct people. But no person, not even blockchain itself, can tie those conversations to the identical wallet seed. Your social graph is mathematically splined due to design.
8. removal of Metadata as an attack surface
Many regulators and spies say "we don't even need the contents and metadata." They are metadata. People you contact are metadata. Zk SNARKs are distinct among privacy solutions because they disguise data at the cryptographic level. The transactions themselves do not have "from" or "to" fields, which are in plain text. There is no metadata to subpoena. Only the document, and it shows only that a legitimate event occurred, and not the parties.
9. Trustless Broadcasting Through the P2P Network
When you use an VPN You trust that the VPN provider to keep a log of your. When using Tor and trust it to the exit node not to track you. With Z-Text, you broadcast transactions that are zk-proofed to the BitcoinZ peer-to'peer network. A few random nodes. You then transmit the data, and disconnect. Nodes can learn nothing since this proof doesn't show anything. There is no way to be certain that you're who initiated the idea, as you might be providing information to someone else. The network becomes a trustless source of information that is private.
10. The Philosophical Leap: Privacy Without Obfuscation
They also mark an evolutionary leap in philosophy from "hiding" from "proving by not divulging." Obfuscation tools recognize that the truth (your Identity, your IP) is dangerous and must be kept secret. ZkSARKs realize that the fact doesn't matter. A protocol must only understand that you're registered. The change from reactive disguise into proactive obscurity is one of the fundamental components of the ZK protection. Your identity, IP address and location are not concealed. They are simply unnecessary to the role of the network hence they're not ever requested and never transmitted or made public. View the top messenger for blog tips including encrypted message in messenger, messenger to download, encrypted message in messenger, message of the text, messenger text message, message of the text, encrypted messages on messenger, text messenger, encrypted text, text messenger and more.

Quantum-Proofing Chats: What's The Reason? Z-Addresses & Zk-Proofs Cannot Withstand Future Decryption
Quantum computing is often discussed in abstract terms -- a futuristic boogeyman that will break all encryption. However, reality is more complex and urgent. Shor's algorithm by a powerful quantum computer, might theoretically break the elliptic curve cryptography system that safeguards a large portion of the internet and other blockchains today. However, not all cryptographic methods are as secure. Z-Text's underlying architecture, built on Zcash's Sapling protocol and zk-SNARKs contains inherent properties that resist quantum decryption in ways that traditional encryption does not. This is due to the fact that what will be revealed as opposed to what's secret. In ensuring that your private keystrokes are not disclosed on blockchains, Z-Text will ensure that there's nothing that quantum computers are able to penetrate. Past conversations, your account, and identity remain sealed, not by sheer complexity but also by its mathematical invisibility.
1. The Principal Vulnerability: Exposed Public Keys
To appreciate why ZText is quantum-resistant, you must first know why many systems are not. As with traditional blockchain transactions your public-key information is made available whenever you make a purchase. A quantum computer could take that exposed public key and employ Shor's algorithm to determine your private key. Z-Text's encrypted transactions, utilizing address z-addresses will never reveal your public keys. Zk-SNARK confirms that you hold the key and does not divulge it. The public key remains forever obscure, leaving the quantum computer nothing it can attack.
2. Zero-Knowledge Proofs, also known as information minimalism
The zk-SNARKs inherently resist quantum because they count on the difficulty of problems that can't be too easily resolved by quantum algorithms as factoring, or discrete logarithms. And, more importantly, the proof is not revealing any data about the witness (your private key). Although a quantum computer could break these assumptions of the proof's foundation, the proof would not have any information in its possession. The proof is one of the cryptographic dead ends that validates a declaration without including any of its content.
3. Shielded addresses (z-addresses) as defuscated existing
A z-address from Z-Text's Zcash protocol (used by Z-Text) will never be recorded onto the Blockchain in a way linking it to transaction. When you receive funds or messages, the blockchain records that a shielded pool transaction was made. The specific address of your account is hidden in the merkle tree of notes. Quantum computers scanning Blockchains can only view trees and proofs, not leaves and keys. It is encrypted, but not observationally, making it invisible to retrospective analysis.
4. "Harvest Now" defense "Harvest Now, Decrypt Later" Defense
One of the greatest threats to quantum technology today isn't an active attack rather, it is a passive gathering. Attackers can pull encrypted information from the internet and store it in the hope of waiting for quantum computers to develop. With Z-Text this is an attack vector that allows adversaries to access the blockchain in order to gather all shielded transactions. However, without access to the viewing keys in the first place, and with no access to the public keys, they are left with zero information to decrypt. Their data is the result of proofs that are zero-knowledge created by design include no encrypted data they are able to crack later. This message is not encrypted in the proof. Rather, the evidence is merely the message.
5. Important to use only one-time of Keys
In a variety of cryptographic systems, reusing a key creates more visible data that can be analysed. Z-Text is based upon the BitcoinZ blockchain's application of Sapling and encourages using of diverse addresses. Each transaction has an illegitimate, unique address which is created by the same seed. So, there is a chance that one address could be compromised (by an unquantum method) while the others are completely secure. Quantum resistance gets a boost from that constant rotation of the keys which limit the impact of one cracked key.
6. Post-Quantum Assumptions in zk-SNARKs
Modern zk-SNARKs typically rely on the elliptic curve, and are theoretically susceptible to quantum computer. The specific design used in Zcash or Z-Text has been designed to be migration-ready. It is intended to eventually support post-quantum secure Zk-SNARKs. Since keys aren't publicly available, changing to a new proving system can happen at the protocol level, without forcing users to reveal their data. The shielded pool architecture is advanced-compatible with quantum-resistant cryptography.
7. Wallet Seeds and the BIP-39 Standard
Your wallet's seed (the 24 characters) cannot be hacked similarly. The seed itself is simply a huge random number. Quantum computers aren't significantly capable of brute-forcing large 256-bit random numbers compared to classical computers because of the Grover algorithm's weaknesses. The issue lies with the generation of public keys using the seed. Through keeping these keys obscured by using zkSNARKs seed will remain secure when it is in a post-quantum era.
8. Quantum-Decrypted Metadata. Shielded Metadata
Though quantum computers could cause problems with encryption but they are still faced with the fact that Z-Text hides metadata within the protocol. The quantum computer may inform you that a particular transaction happened between two individuals if they had their public keys. However, if the keys aren't revealed as well as the transaction is an zero-knowledge verification that does not contain address information, Quantum computers only know that "something happened in the shielded pool." The social graph and the timing along with the frequency, are largely unnoticed.
9. Merkle Tree as a Time Capsule. Merkle Tree as a Time Capsule
ZText stores all messages inside the merkle tree in blockchain's protected notes. This is an inherently secure structure from quantum decryption, because in order to locate a particular note in the tree, one needs to know its note's commitment to the note and where it is within the tree. Without a key for viewing, any quantum computer will not be able to recognize your note from millions of others that make up the tree. The computation required to look through the whole tree in search of a particular note is insanely big, even for quantum computers. It also increases with every block added.
10. Future-proofing Using Cryptographic Agility
Last but not least, the most significant factor in Z-Text's quantum resistant is its cryptographic aplomb. The system is built using a blockchain protocol (BitcoinZ) that can be modernized through consensus in the community cryptographic fundamentals are able to be switched out when quantum threats materialize. Customers aren't bound by a single algorithm forever. Since their personal history is covered and their key is stored in their own custodial system, they are able to move into quantum-resistant new curves, but without sharing their history. The structure ensures your conversations are safe not only against the threats of today yet also for the ones to come.